A Proactive Guide to Fighting Ransomware


The Harvard Business Review pointed out that in 2020 ransomware attacks grew 150% over 2019. One reason is that the attack surface, the systems that are accessible and could be compromised, is massive and keeps growing. The IT footprint of small and medium-size businesses (SMBs) may present dozens or hundreds of vulnerable endpoints and pieces of software. For larger companies, the systems in the attack surface may run into the thousands.
Billions of dollars' worth of confidential and potentially marketable data behind firewalls represent a juicy target for cybercriminals. Today's cybercriminal organizations are hierarchical, well organized, and they leverage modern business models such as ransomware as a service to proliferate their malware.
The more companies pay ransoms, the more incentivized cybercriminals become. In the same article, Harvard Business Review noted that the amount paid by victims of these attacks increased more than 300% in 2020.
At some point, if you're a big enough target, somebody is probably going to have some success in a ransomware attack on at least part of your environment. The key is to make sure that any such breach is quickly contained and has the smallest possible impact.
The good news is that there are proven methods to provide protection. My session at Hitachi Social Innovation Forum 2021, Achieve Your Cybersecurity Goals with AI, ML and Data Center Automation, offered a crash course designed to help organizations be better informed and better prepared. The steps an organization takes today will determine the ultimate cost of the next attack.
Historically, threat actors can be separated into roughly two categories, though the lines are blurring a bit as the automated tools available to cyber-criminals become more sophisticated. Cybercrime syndicates are the low-level organized crime of the internet. They succeed mainly against vulnerable SMBs by indiscriminately using automated attacks to overwhelm security in search of vulnerabilities. Enterprise-level environments are generally better prepared to detect and contain these unsophisticated attacks. The most dangerous threats to enterprises are advanced persistent threat actors, or APTs — the apex predators of the cybercrime world. These actors may take months to reconnoiter and then manually operate their attacks, adjusting tactics with precision as they encounter defenses and new vulnerabilities.
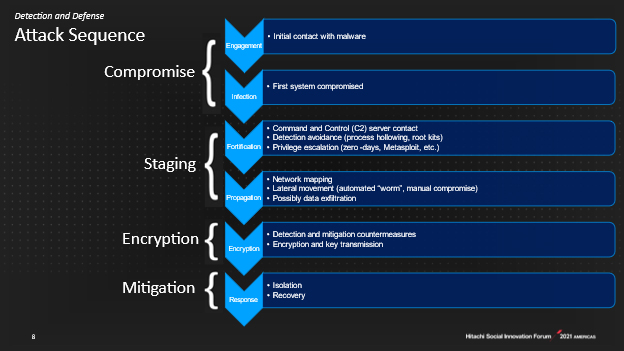
Understanding the four stages of typical ransomware attacks provides the framework against which an organization can map its defenses. Let's examine each stage of the attack sequence and consider the technology and strategic considerations available to an organization.
[legend] worm = write once read many
Attacks begin when a software vulnerability is exploited, someone clicks a link or visits the wrong website. The majority of breaches are from endpoint vulnerabilities and poorly protected or configured remote desktop ports. The enormous number of people now working from home exacerbates this problem. Other types of attacks include phishing campaigns and account takeover techniques, such as password spraying, brute forcing, and social engineering.
The guidance here is to harden endpoints, aggressively patch everything, and perform penetration tests to identify vulnerabilities. Make passwords long and complex. Educate users to get them actively engaged in their role in security. Unfortunately, as FBI Supervising Field Agent Joel DeCapua made abundantly clear in his presentation at the 2020 RSA Conference, there are just too many attackers out there, far too many vulnerable endpoints, and too many susceptible employees. Organizations will remain susceptible to malware despite their best efforts and need to prepare for the next stage, where the problem propagates across systems.
With access to systems achieved, the malware runs processes to secure its beachhead and establish persistence across reboots. It will contact its command and control infrastructure and then run exploits to escalate privileges and gain access to other machines. Through network mapping, malware propagates laterally to other servers in the environment. The crown jewel for a malware attacker is the domain controller, unlocking access to the entire environment.
Adopting a zero trust model can help. Zero trust means that no one gets access permission to anything, anywhere, without good reason. When they do, access is on a timer so there is nothing left for an attacker to scoop up down the road. Ultimately, defense at this stage is all about constantly monitoring networks and systems for anomalies in account access times and activity, process activity, network activity, connections, file access activity, and how data is moving. With thousands of users, systems, endpoints, millions of data points to be collected, correlated, and compared, processing this much data is literally beyond human capability.
That is exactly the type of task that machine learning (ML) is ideally suited to carry out. ML gathers relevant metrics, then builds a baseline profile of the environment. It then watches tirelessly for deviations and scores them as it occurs. It also learns from human operator responses to better predict future attacks. ML-based Endpoint Detection and Response (EDR) and Network Detection and Response (NDR) solutions are available on premises and as a service, with telemetry sent to cloud services for analysis. There, big data analysis can combine data from multiple customers to improve accuracy.
The malware is now fully at war, shutting down your antivirus, monitoring, and backup systems. Often, as a pre-cursor to the encryption event, it will search out and attempt to encrypt backups to mitigate recovery strategies. As encryption occurs, the malware communicates keys to the attacker's command and control infrastructure.
AI and ML can both offer some help in containing a threat. They can detect some processes that look like encryption and possibly shut down activities that are changing files. They may also be able to help to segment and isolate parts of the network.
But at this point, the horse has kind of left the barn. While the attack may be contained or slowed, some data is encrypted, and it is probably something the organization needs.
If the organization has prepared well, it should have the opportunity to isolate the attack, perform recovery, and get back to business. Consider a cyclical, seven step program, performed annually at a minimum, that includes:
According to Sophos, paying a ransom to get your data back is a gamble at best: Most victims are unable to recover some or all of their data. In fact, Sophos reports that 92% of those who paid ransom lost some data, 50% lost at least a third, and 4% lost it all. Effective mitigation is the only trusted recourse to get data back. Mitigation requires a strong plan and robust architecture that makes it possible to retrieve data from backups. (See "Overcome Risks of Ransomware With Hitachi Content Platform Portfolio" for a plan for creating robust backups.) Having immutable copies is the last, best chance at restoring operations. A truly immutable approach works at the storage level, which is the lowest level of application and IT stacks, and cannot be defeated with any existing, on-site authentication.
Automated storage-based copies are an excellent strategy, as they offer low visibility to attackers and strong immutability on the copies regardless of access levels. For SMBs, basic storage snapshots with strong locking protection offer resilience and quick recovery against the most likely threats. Data center automation here manages the snapshot creation schedule and the locking regime, as well as recovery sequences.
The enterprise requires more enhanced protection. Techniques may include replication to other locations, replicating to air gap arrays with no host connections, a dedicated control plane network, IP whitelisting, minimal data paths, AI or ML to detect anomalies, and other trusted computing block concepts. While more complex, these architecture approaches can offer protection against sophisticated, apex attackers.
Effective cybersecurity, particularly defending against ransomware, depends on preparation. (See Hitachi Vantara's joint session with Commvault on Overcoming the Risks of Ransomware for more detail.) Criminals can pivot in hours or days to newly documented exploits and vulnerabilities, while an enterprise is still patching its systems to the previous threat. Governments and corporations can't move as fast as the attackers. While there are no silver bullets, AI and ML enable the critical advanced, behavior-based monitoring at scale that can help.

Mark Hickey is responsible for understanding customer needs, industry trends and the competitive landscape to deliver high-value solutions. He has +30 years' experience in software development, architecture, solution design, managed services and storage and backup delivery.